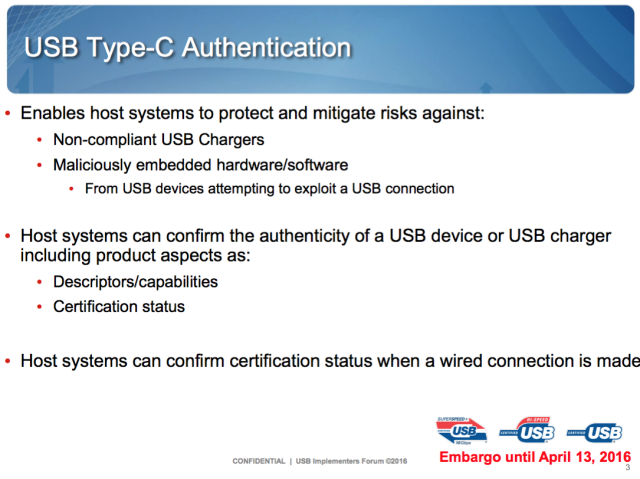
El USB-IF crea la especificación USB Type-C Authentication para detectar cables 'peligrosos' - ITespresso.es

USB Type-C Authentication Program to restrict usage of uncertified USB-C chargers and accessories - MSPoweruser
The USB Type-C Authentication Specification Aims to Prevent Damage from Non-Compliant Cables and Adapters - CNX Software

USB Type-C Authentication Program: il nuovo programma per accertare l'affidabilità dei dispositivi - IlSoftware.it